PHYSICAL SECURITY OF YOUR DATA CENTER


A world of information on earth
With an increasing dominance of cloud services in existing business operations, at the end of 2020, the virtual weight of all the information in the world was 44 zettabytes (trillion gigabytes), a figure featuring 21 zeroes, and growing… 44,000,000,000,000,000,000,000 bytes
Not surprisingly, around 50 percent of all corporate data is stored in the cloud. It's gigantic!In 2020, the global cloud computing market was valued at $371.4 billion, and it is estimated that by 2025 it will rise to a staggering $832.1 billion - Source Wikipedia
WHY PHYSICAL SECURITY IS SO IMPORTANT FOR A DATA CENTER
Whether a data center is used mainly for storage, disaster recovery, or supporting applications, its computational workloads are the backbone of the businesses it serves. In addition, a company's sensitive information and business-critical applications are a treasure trove of opportunity for hackers and other threats.
Data centers are a trusted component of an organization's infrastructure. Many companies depend on their data center assets to provide a safety net when all else goes wrong. In this way, a secure data center ensures business continuity and gives its users confidence that they can focus on growing their businesses without worrying about the safety of their digital assets.
WHAT SHOULD YOUR DATA CENTER SECURITY PLAN INCLUDE?

Perimeter Security
The objective is to protect the building by discouraging, detecting, and delaying any unauthorized people as much as possible. Proper fencing, gates and doors with video intercom systems so that security can see and identify who is requesting to enter. Proper perimeter lighting is not only a deterrent, but helps with your video surveillance coverage. In addition, video content analytics detect suspicious behaviour and include face recognition to track movements and license plates. It is also important to make sure you have camera coverage on your roof and loading docks.
People with no access card must request access prior to arriving at the Data Center. They must present a photo ID and an authorization to enter the building, which must be granted by security management. All accesses granted should be recorded and traceable. Make sure these visitors are always accompanied and only have access to the assigned area for service.
24/7 Security Guards are normally situated at the front entrance of the building greeting everyone who enters. These agents also routinely patrol the Data Center and monitor the videos of cameras inside, reporting any breach immediately.

All employees should also pass a two-factor authentication with biometrics or IRIS scan to continue moving through the datacenter, and must always carry with them their ID badge. These employees are only allowed onto the floor section of the building that has been pre-approved.
Facility Controls
Your access control system is your safety net in case you have a perimeter breach. Biometrics, and iris access systems can restrict access to non-authorized people. Include an access control system with an anti-tailgating/anti-pass-back facility to permit only one person to enter at a time a single entry point into the facility.
A state-of-the-art video surveillance system with continuous recording will also help monitor effectively and help you learn from any incidents that occurred. Installations of turnstiles are highly effective to prevent tailgating at the access stage.

Even with the best systems in the market, you must have a trained guard monitoring them to be effective. Engaging a professional security team to guard, monitor and report all non-respected policies, issues with compliance and suspicious behaviour to security management is essential. Responding to and alerting facility technicians of any alarms with temperature and humidity controls, air conditioning controls, fire alarm and smoke detection systems is essential and part of their training and illustrate why they are a very crucial part of operations.
Computer Room Controls
Only people with the proper clearance should be allowed into control rooms or computer rooms, also called PODS. Greeted by another security guard, in most of the cases, you are required to pass a full body metal detection screening. Inside the computer control rooms, there are locked cabinets keeping the servers secure. To reduce the risk of unauthorized data entering or leaving the datacenter without permission, only approved devices can make their way into the datacenter floor.

Additionally, video cameras monitor the front and back of every server rack. When exiting the datacenter floor, one must again undergo a full body metal detection screening. In some cases, they are also required to pass through an additional security scan when exiting the datacenter.
Audit Practices
Conduct regular audits to double-check that you and your team are on top of things, including all suppliers, cleaning maintenance crew and security agents that have access to the Data Center.

Internal audits verify the implemented systems and processes and identify any vulnerabilities in the data center facilities to ensure security. Guard will also verify if access control systems, video surveillance cameras and electronic locks are functioning and are being maintained. They will identify any systems requiring maintenance or repair as well as any discrepancies found, recording the incident with date and time. Identify any weakness or oversight in equipment within areas that were overlooked in the construction or renovations.
It is also important to enforce security measures with employees and suppliers periodically as well as exchange ideas and recommendations. The more awareness of your security objectives, the more secure the Data Center will be. Ensure that your team receives adequate training on the security measures to be followed and make sure they get it and understand the consequences of non-compliance.
WHERE TO PLACE YOUR DATA CENTER
You’ve heard the term “location, location, location” in the retail world… well the same importance should be emphasized for Data Centers. Whether you are thinking of building a brand-new facility or remodeling an existing one, your security plan begins by properly studying the location. Hazardous materials within a close perimeter, right under an airplane flying path, natural weather conditions, are some of the risks you may want to study and research before you settle on or purchase land to build.

New Building
A Physical Security Manager is the ideal candidate to implement a security plan and strategy on a State-of-the-Art new construction. They have the opportunity to be present from the design all the way to overlooking the construction of the building, such as the size of the fence, depth of walls and roof, among others. If space of land is not limited, generators and ventilations systems can be on ground level. The opportunity to do a selection of the latest technologies such as Video surveillance, access systems, turnstiles and other security systems needed to meet compliance.
Existing Building
Taking over an existing building can be challenging especially when you need to take an audit of the building infrastructure or any security systems in place. An engineering plan and space design of the data center is required and necessary. Structure reinforcements must be made if equipment is needed to be installed on the roof, such as ventilation, heating and air conditioning systems. Particular attention must be given to fire detection systems especially in the server areas. Purchase of additional proper security systems such as video surveillance, access control systems, biometric and perimeter monitoring systems may be needed to meet compliance and optimal protection.
ADDITIONAL PHYSICAL SECURITY CONSIDERATIONS
Data Centers are always under threat due to the amount and valuable information they house. Whether it's by accident or maliciously done, a breach of unauthorized access accounts for about 18 percent of all breaches worldwide and reportedly costs the industry more than $400 billion annually.
60% of data center security threats are from an internal source. Whether they are unintentional or malicious, it is very critical to ease vulnerabilities from within by controlling the level of access that technicians have. In your Data Center Management Software or your DCIM solution, limit your employees' access to areas of your data center, devices, and what features they can use.
Background checks
Knowing that 60% of security threats come from Data Center employees themselves, you cannot be too careful about who works in your Data Center. Pre-employment background checks are now nearly universal, but you should also run background checks on vendors and contract employees who have access to data.
On-site security team
Security measures such as video or physical surveillance and checkpoints are integral to comprehensive Data Center security, but security staff need to be on site around the clock to reduce and respond to threats. Security teams should also conduct routine video and foot patrols as a constant reminder to would-be intruders that your data center is protected.

Employee procedures
When an employee with access privileges to secure areas of your data center leaves the organization, there needs to be a procedure in place to remove their permissions. This can include changing access codes, updating access lists, revoking credentials, collecting keys, or removing biometric data. Providers should have strict controls for who can access your data and should be notified when an employee leaves the organization.
Video surveillance
A primary system of Data Center security, video surveillance is an extremely valuable and cost-effective tool to reduce security threats. Visible imaging cameras are common for detection and observation. Infrared cameras are best in low-light environments, and thermal cameras are extremely difficult to bypass. Use the DCIM software to take video surveillance to another level from IP and USB cameras one step further and add multiple feeds to your dashboard so you can monitor multiple areas remotely.
One Final Note… Be proactive!
Don't wait until the aftershock of a breach or intrusion to protect the critical assets in your Data Center. Get centralized, modernize data security management with a second-generation DCIM solution to reduce the risk to your data center. Data Centers face new threats to physical security every day so having a comprehensive security plan in place, performing a periodic audit of your facilities and addressing all the issues uncovered is essential.
With the world’s information in digital format continuously growing, data centers will increasingly be needed, maintained and secured for a long time to come!
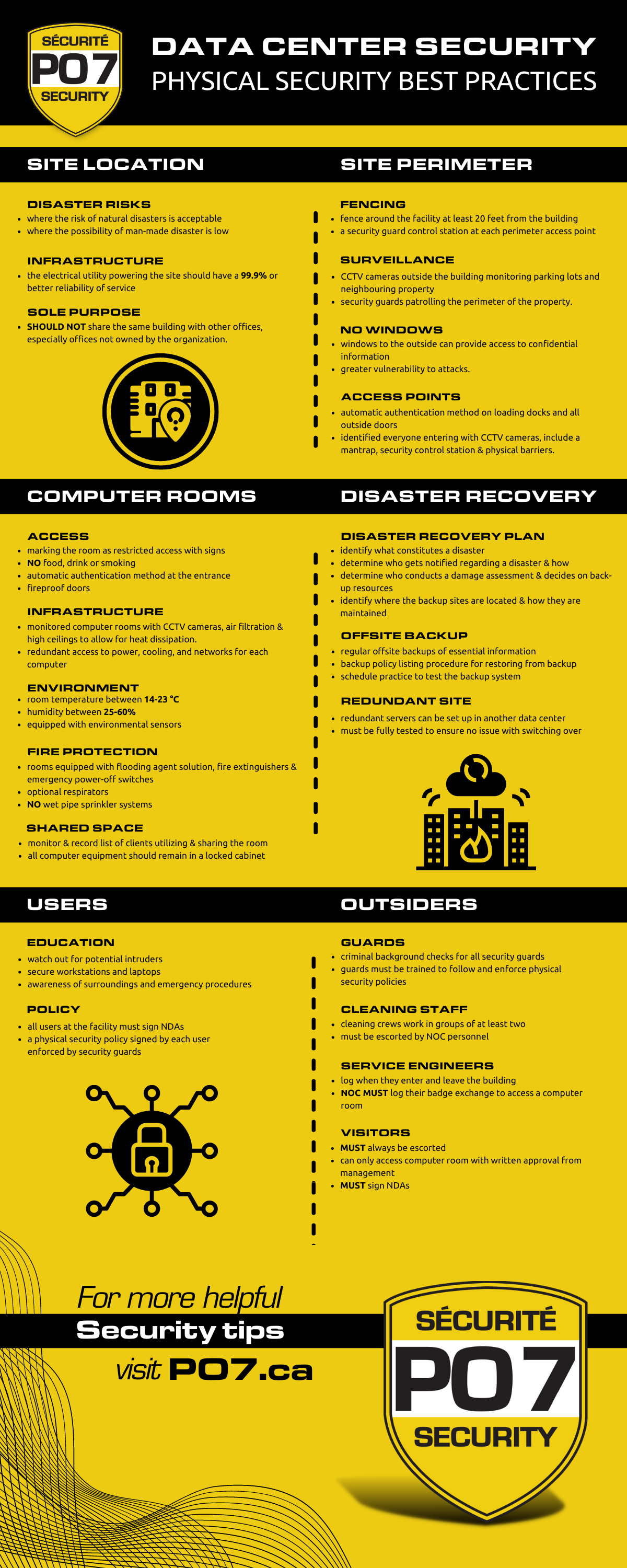
Here’s a helpful infographic showcasing my Data Center Physical Security Best Practices
Our Services include: Security Guards | Security Risk Management | Loss Prevention | Security Training
We serve clients across Montreal, South-Shore & Sorel-Tracy, Quebec.
